Mobility
4 Case Studies Show How IT Can Improve Employee Experiences
Trends Are Shifting, and Expectations Are Rising Over the past 10 years, the way people use technology...
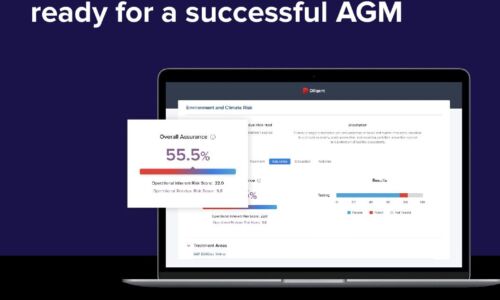
4 tips to ensure your board is ready for a successful AGM
The 2022 AGM season is on course to see unprecedented levels of challenge for boards and businesses....

Box and ECM: Key integrations that drive digital transformation
Box and ECM: Key integrations that drive digital transformation Legacy ECM solutions simply can't keep...

Data Loss Prevention and Digital Transformation
Today's digital age has produced unprecedented amounts of data. Much of this data is considered sensitive,...

Six Top Trends and Predictions for Data, Analytics, and AI in 2021
Although making predictions about the future is difficult even under the best of circumstances, it's...
The Definitive Guide To SASE
What is Secure Access Service Edge (SASE) and why do you need it? Download the new guide to learn how...

GigaOm Radar for Phishing Prevention & Detection
Get your complimentary copy of this independent GigaOm Research report, which analyzes positioning and...
CIO Essential Guidance: Intrinsic Security
Despite massive spend to protect enterprise digital assets, security breaches are still on the rise....

5 signs your SaaS company needs to improve its usage data management
If your SaaS company offers usage-based pricing, there's a good chance you've built an in-house solution...
Digital Acceleration in the line of coronavirus
A global survey of 600 technology decision-makers conducted by MIT Technology Review Insights, in association...

Powering your organisation with an agile productivity stack
I wonder where our important files have run off to today.' When you've got one seamless, secure platform...
Sign up for FinTech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.