Software
The CIO’s Guide to Transformation with AppExchange
A huge part of a CIO's role is 'keeping the lights on'. They are responsible for making sure systems...

Pure Unified Fast File and Object Storage
For businesses to maximize the value of their data, they first need to rethink their infrastructure—with...

Threats to DNS Are Threats to Your Business. What You Can Do
DNS is a foundational part of the internet, and its hierarchal structure is well known and understood....
Introduction to AWS Security
Raise your security posture with AWS infrastructure and services. AWS's approach to security, including...
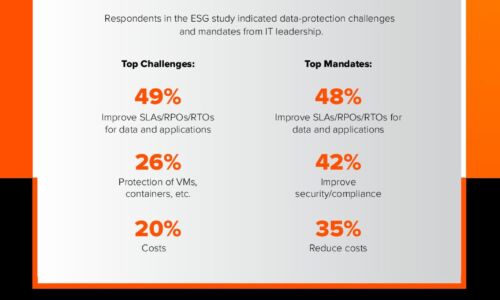
Close the Data Availability Gap
A recent ESG survey of over 1,000 global IT decision-makers found that 82% of enterprises are facing...
The state of industrial security in 2022
Security for the industrial internet of things (IIoT) and operational technology (OT) is in its infancy...
Economist: Signals and Noise: The New Normal in Cybersecurity
Cybersecurity is a top priority for Boards and the C-Suite. Strengthen your security posture with executive...

The State of SD-WAN, SASE and Zero Trust Security Architectures
The purpose of this research is to learn important information about the use of Software-defined Networking...

Run your Windows workloads on AWS
The best platform for Windows Server and Microsoft SQL Server Customers have been running Windows workloads...
NETSCOUT Threat Intelligence Report 1H 2020
COVID-19 has driven both workforces and consumers online – but the lockdown also saw DDoS attack frequency...
The Essential Guide To Machine Data
Machine data is one of the most underused and undervalued assets of any organization, yet it contains...
Sign up for FinTech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.