Applications
How to Build Your Microsegmentation Strategy in 5 Steps
A breach to your organization's network is not a question of if, but when. Are you prepared with a micro-segmentation...
Everything You Need to Know About Electronic Signature
Stacks of papers that need to be signed, filing cabinets full of paperwork— these are quickly becoming...

Forrester Total Economic Impact of Tanium
The Forrester Consulting Total Economic Impact™ (TEI) study commissioned by Tanium helps technology...

Inherent Vulnerabilities Harming Telecommunications Companies
Telecommunications companies are among the most targeted companies in the world, attracting the most...

PHP, MySQL, and JavaScript All-in-One For Dummies
Get the basics on four key web programming tools in one great book! PHP, JavaScript, and HTML5 are essential...

For digital sovereignty and transparency in the cloud
Shared use of infrastructure not only saves resources but also enables companies to push ahead with digitalisation...

Don't pay the ransom
In simple terms, ransomware is malicious software that either encrypts your data or otherwise stops you...
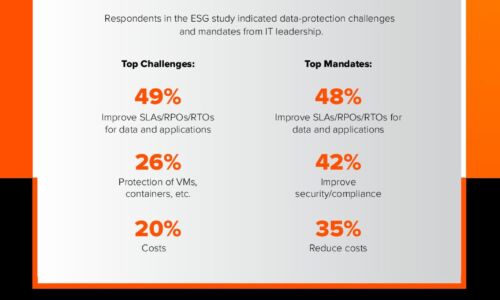
Close the Data Availability Gap
A recent ESG survey of over 1,000 global IT decision-makers found that 82% of enterprises are facing...

Efficacy of Micro-Segmentation: Assessment Report
Micro-segmentation is an essential security control that prevents the lateral movement of attackers....

ERP Modernization Is Business Transformation
Learn how a cloud-based ERP system can help your organization get better business insights, increase...
Hidden Costs of Endpoint Security
When it comes to endpoint security, CISOs are in a bind. Most assume that endpoints will be compromised...
Sign up for FinTech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.