Latest Whitepapers
Better Security. Fewer Resources.
When you consider the number of headlines that appear on a regular basis about major data breaches —...

Why Today's Business Applications Belong in the Cloud
Has there been a more exciting time to be at the forefront of business? It's unlikely. According to a...

Healthcare IoT, the RX for Providers and Patients
Healthcare providers have a lot on their plates. Costs are always on the rise, and staff shortages put...

An IT Strategy to Support the Modern Analytics-Driven Business
For IT organizations, the requirement for high-performance systems and analytics tools that work with...

Drive CPG Revenue through Digitalized B2B E-Commerce Ordering
E-commerce has been shaping buying trends for the past 20 years. But surprisingly, the global B2B e-commerce...
Common Browser Isolation challenges, and how to overcome them
A growing number of security teams are implementing a Zero Trust security strategy, in which no application,...

Advanced Threat Research Report October 2021
As 2021 progressed through its second quarter and into the third, cyber criminals introduced new—and...

Unmasking BEC and EAC
Whether they result in fraudulent wire transfers, misdirected payments, diverted payrolls, supply-chain...
The Anatomy of Account Takeover Attacks
Bad bots are on every website with a login page. Even yours. Hackers and fraudsters use bots to validate...
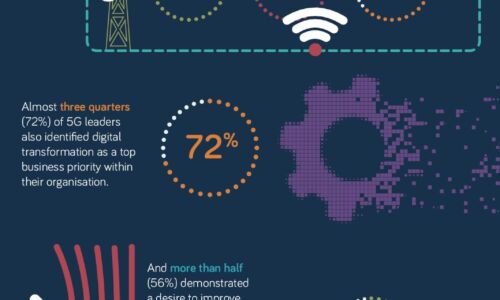
What makes a 5G Leader?
With 5G a still nascent technology, opportunity remains for businesses to accelerate adoption of this...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.