Virtualization
A Five-Step Plan to Move Your Apps to the Cloud
Cloud applications, platforms, and services are changing the way enterprises compete for customers. The...

GigaOm Radar for Data Storage for Kubernetes
Kubernetes adoption is quickly accelerating, and enterprises are now in a transition phase. In the last...

Database Solutions Pocket Book
Given the fast pace of modern business, traditional enterprise infrastructure is ill-suited to meet the...
Cloud Computing for Dummies
Cloud computing is a topic that technology pros need to know to stay ahead of the computing game. Cloud...

Edge Computing in Telco Networks: Gaining the Competitive Edge
Earlier this year, Wind River® teamed up with F5, Schneider Electric, and Heavy Reading on a global...
Data In, Value Out
In today's increasingly data-driven business landscape, the companies who succeed are typically those...
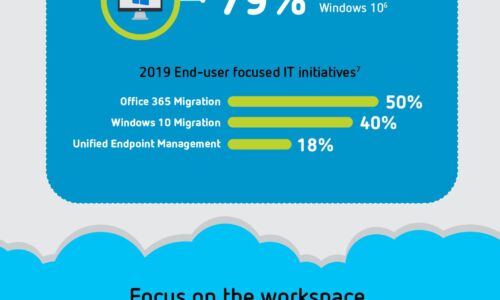
Digital Transformation: A Look Ahead
Digital transformation is reshaping organizations into digital businesses. Organizations are focused...

Not All End User Experience Monitoring Solutions Are Created Equal
Digitization has undoubtedly changed the way companies do business with their customers, partners and...
Fujitsu Mobility Solutions For Your Classroom
In recent years, data has had a resurgence being labeled as one of the newer trends in education. The...
Your Data. Their Cloud.
In today's organizations, digital transformation is a vital imperative—and cloud services offer a proven...
Sign up for FinTech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.