Server

Q4 in review: The latest DDoS attack vectors
2021 witnessed massive DDoS attacks that demonstrate a trend of intensifying cyber insecurity that affected...
Transforming the SOC: Building Tomorrow's Security Operations, Today
When you think of a security operations center (SOC), what comes to mind? Is it an organized team of...
Achieve Cloud Security Cost Savings Through SIEM Optimization
Tame Rising SIEM Costs and Complexity Do you worry that your SIEM is falling behind on efficiently handling...

5 New Rules to Protect Your Data Centers and Cloud Environments
In this white paper, we look at five new rules to secure data centers and cloud environments. These rules...
Identity is Key to Stopping These 5 Cyber Security Attacks
A secure enterprise is a successful enterprise. Security threats are a massive burden for most organizations—but...
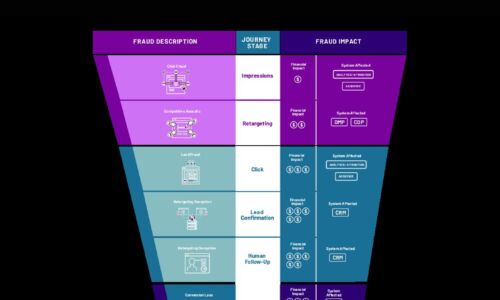
Cybercrime Threatens the Digital Funnel
Cybercriminals are employing new attack methods on new digital surfaces, including digital marketing....
Cyber-resiliency Maturity in Data Storage
As the scale and volume of cyberattacks continues to rise, application environments become more dispersed,...

Multi-cloud Load Balancing for Dummies
Legacy hardware-based load balancers don't meet modern enterprise application delivery requirements in...

Dell Docks: A Dock For Every Need
Dell Docks- giving you more power to get ahead. Designed to efficiently connect to displays, keyboards,...

A Blueprint for Containers and Orchestration Best Practices
Containers enable agile deployment capabilities, requiring less coordination and oversight than on-premise...
Cyberthreats: A 20-Year Retrospective
Annual threat reports provide an opportunity to look back at significant events of the past 12 months...
Sign up for FinTech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.


