Security Solutions
The Anatomy of an Insider Threat Investigation: A Visual Guide
For decades, perimeter-based security strategies have been the starting point for most cybersecurity...
Is Your WAF Keeping Pace with Today’s Advanced Threats eBook
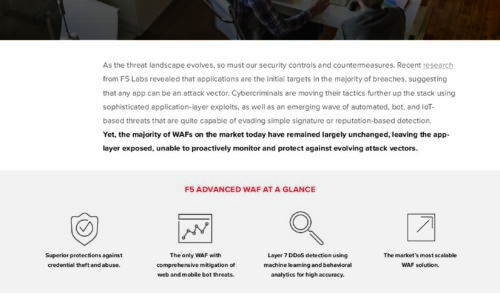
As the threat landscape evolves, so must our security controls and countermeasures. Recent research from...

Choose the WAF That’s Right for You
Despite the industry's best efforts to bolster secure application development practices, the growing...
32 Security Experts on Changing Endpoint Security
For many companies, the modern business environment has become a mobile workplace in which employees...

Spear Phishing: Top Threats and Trends
Cybercriminals are constantly refining their tactics and making their attacks more complicated and difficult...

Case Study - Malwarebytes Endpoint Protection and Response
Malwarebytes cut potential downtime to a matter of hours rather than weeks. Malwarebytes complements...

The State of Application Security in 2021
Barracuda commissioned independent market researcher Vanson Bourne to conduct a global survey of 750...
The Anatomy of an Insider Threat Investigation
For decades, perimeter-based security strategies have been the starting point for most cybersecurity...

Sharing the Workload of Workload Security
Security teams need the help of IT operations to secure workloads IT admins and security teams both play...
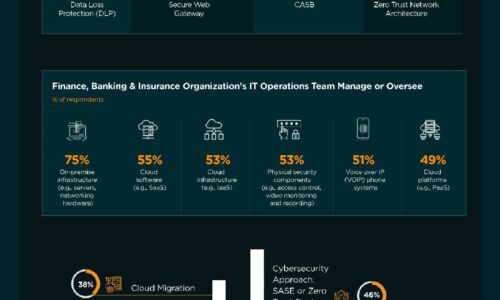
Finance, Banking & Insurance Industry | State of Cybersecurity 2021
This infographic by ISACA and HCL Technologies discusses the state of cybersecurity within the finance,...
What Today's Retailers Need in a Security Architecture
Retail cybersecurity in the age of the omnichannel customer experience requires CIOs and vice presidents...
Sign up for FinTech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.