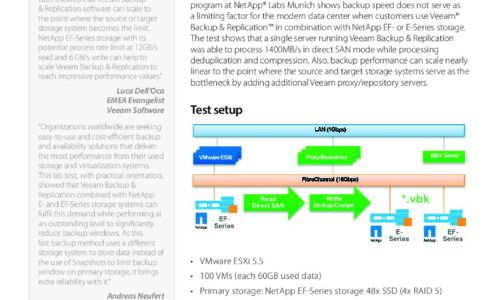
RAID
Upgrade to State-of-the-Art Log Management
Most log messages traditionally come from three types: system logs of servers, network devices, and applications....
MandA IT Integration Checklist: Active Directory
If your organization is involved in a merger and acquisition, the impending IT integration project might...

Key Storage Considerations in Determining Optimal Workload Placement
In early 2020, IDC performed in-depth primary research on how organizations determine workload placement...

Top Ten Tips When Buying A Raid Adapter
RAID (Redundant Array of Inexpensive Disks) is a data storage structure that allows a system administrator...

Cyber Attack Trends: Check Point's 2022 Mid-Year Report
The war in Ukraine has dominated the headlines in the first half of 2022 and we can only hope that it...

Cyber Attack Trends: Check Point’s 2022 Mid-Year Report
The war in Ukraine has dominated the headlines in the first half of 2022 and we can only hope that it...
Unlocking collaboration in higher education
Collaboration and knowledge sharing are pillars of higher education. Instead of working in silos detached...
How media companies thrive in the digital age
As technology and media continue to evolve at a rapid pace, publishers, producers, editors, and filmmakers...

Ransomware Survival Guide
Be Ready for Ransomware Ransomware is an old threat that just won't go away. While overall volumes have...

The Total Economic Impact™ Of Dell EMC Servers For SAP
To run a digital business that is Intelligent and agile, your enterprise requires an IT landscape capable...
Sign up for FinTech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.