Network
Security Control Guide: Hardened Services Guide
System Hardening is the process of securing a system's configuration and settings to reduce IT vulnerability...

Reduce Cloud & Container Complexity, Improve Cost Efficiencies
Visibility into ever-growing containerized environments, better application context for alerts, faster...
Enhancing Microsoft Security with HelpSystems Email Security
Learn how HelpSystems Email Security can enhance Microsoft 365. Microsoft 365 offers tiers of security...

2021 Norton Cyber Safety Insights Report Global Results
Prepared by the Harris Poll on behalf of NortonLifeLock, we consider: 1. Cybercrime: Incidence, Impact,...
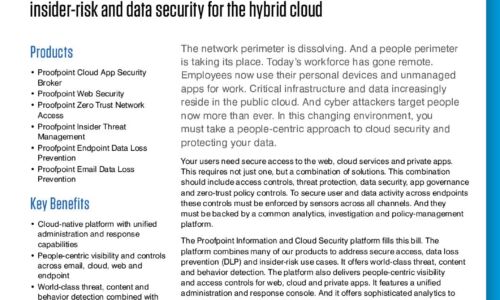
Proofpoint Information and Cloud Security Platform
The Proofpoint Information and Cloud Security platform combines many of our products to address secure...

Encryption Is Now a Trojan Horse: Ignore It at Your Peril
The game of leapfrog between hackers and data security professionals continues. No sooner do organizations...
A Buyer’s Guide to Optimizing Remote Employees’ Extended Network
The shelter-in-place mandates put in place earlier in 2020 sent most employees home, and for the next...
The Anatomy of Account Takeover Attacks
Bad bots are on every website with a login page. Even yours. Hackers and fraudsters use bots to validate...
Sign up for FinTech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.