Network

Sotero Data-In-Use Encryption
Though encryption is the most effective way to reduce the probability of a security breach, traditional...

IT’s 5 Toughest Work from Home Challenges and How to Solve Them
2020 forced the shift to a hybrid work model Unexpectedly, you found yourself working from home. The...

Building A Better Cloud Begins With Better Infrastructure
The modern enterprise lives in a multi-cloud world, where delivery of infrastructure resources and IT...

An Overview of Insider Threat Management
As organistions move towards a more distributed workforce, the traditional perimeter of the office network...
The Data Breach is Coming from Inside the House
Real-Life Tales of Data Loss, Insider Threats and User Compromise Data doesn't lose itself. People lose...

CISO’s Playbook to Cloud Security
To secure enterprise assets in the cloud, CISO's must address several new challenges unseen in traditional...

Simplified Zero Trust Segmentation with Illumio Core
Modern ransomware is one of the most significant cybersecurity threats to critical services, compute...
Transforming the SOC: Building Tomorrow's Security Operations, Today
When you think of a security operations center (SOC), what comes to mind? Is it an organized team of...
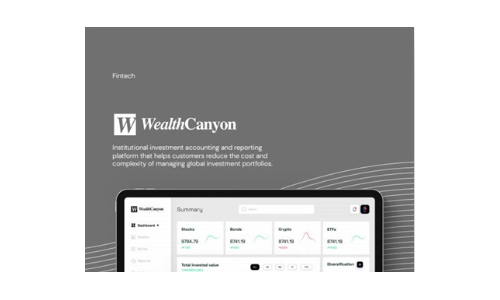
Wealth Canyon
Software companies in the financial industry, such as WealthCanyon, face challenges in collecting and...
Sign up for FinTech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.