Network
State of Ransomware: Invest now or pay later
Ransomware attacks continue at a blistering pace because organizations remain vulnerable to the exploits...
4 Case Studies Show How IT Can Improve Employee Experiences
Trends Are Shifting, and Expectations Are Rising Over the past 10 years, the way people use technology...

Discover How Organizations Speed AI/ML Adoption with Red Hat Openshift
Turn your data into a valuable business asset and a competitive advantage. Artificial intelligence (AI)...
Economist: Signals and Noise: The New Normal in Cybersecurity
Cybersecurity is a top priority for Boards and the C-Suite. Strengthen your security posture with executive...

Use Case-Driven Cloud Security Evaluator Guide
Researching cloud security? Be sure you evaluate yourself and your vendors on the 6 most common cloud...
Upgrade to State-of-the-Art Log Management
Most log messages traditionally come from three types: system logs of servers, network devices, and applications....
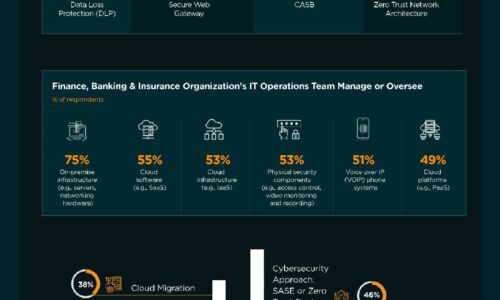
Finance, Banking & Insurance Industry | State of Cybersecurity 2021
This infographic by ISACA and HCL Technologies discusses the state of cybersecurity within the finance,...

3 Ways to Make Cloud Your Business
The role of IT infrastructure and operations leaders has dramatically changed, and cloud evolution continues...

Efficacy of Micro-Segmentation: Assessment Report
Micro-segmentation is an essential security control that prevents the lateral movement of attackers....

Reduce data processing time by up to 50%
As the world around us becomes more digitised, data is becoming more and more important. The problem?...
Sign up for FinTech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.