IT Security

The State of Email Security 2020
Global business is interspersed with a diversity of industrial sectors, united by a single, common communication...

Farewell ISDN. Hello All-IP.
Analogue and ISDN telephony is a thing of the past – telephony today is mostly internet-based. Voice-over-IP...
Transforming the SOC: Building Tomorrow’s Security Operations, Today
When you think of a security operations center (SOC), what comes to mind? Is it an organized team of...
Cloud Computing for Dummies
Cloud computing is a topic that technology pros need to know to stay ahead of the computing game. Cloud...
5 Reasons to Upgrade Your Symantec Email to Proofpoint
Symantec is now part of Broadcom, a semiconductor manufacturing company. For Symantec customers of all...
ServiceNow + Vonage: The Perfect Combo
Video Overview of Vonage Contact Center and ServiceNow - Vonage Contact Center (VCC) for ServiceNow integrates...
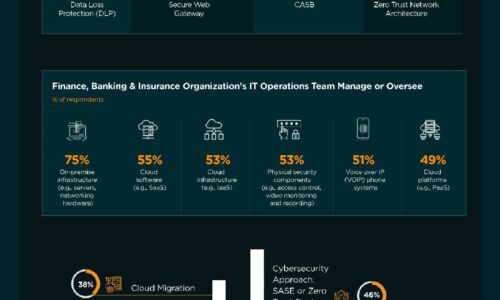
Finance, Banking & Insurance Industry | State of Cybersecurity 2021
This infographic by ISACA and HCL Technologies discusses the state of cybersecurity within the finance,...
Forrester A Practical Guide To A Zero Trust Implementation
Secure Workload Access On Your Journey To Zero Trust Including the licensed Forrester report: A Practical...

Forrester Wave, We're a leader!
VMware Carbon Black Named a Leader in The Forrester Wave™: Endpoint Security Software As A Service,...

Security Starts Here: Privileged Access Management
The threat of a security incident or critical error is very real, and it's something that auditors are...
An Insider’s Look at Enterprise Cloud Adoption
It's a well-known fact that more businesses are adopting cloud computing technologies, and the overall...
Sign up for FinTech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.