Data Center

Finding a platform worthy of your data
Attacks on your data are getting trickier, and insider threats are on the rise. More than half of IT...

Multi-Cloud IT Executive Buyer's Guide
Intentionally establishing a multi-cloud strategy is a powerful way to modernize your IT infrastructure...

Increase the ROI of Inspection Technologies with F5 Orchestrator
Recent analysis by F5 Labs shows that 68% of malware installed through phishing is hiding in encryption....
Protecting the ATM Network with Fortinet
Protecting a network of geographically dispersed automated teller machines (ATMs) is a key challenge...
What Today's Retailers Need in a Security Architecture
Retail cybersecurity in the age of the omnichannel customer experience requires CIOs and vice presidents...
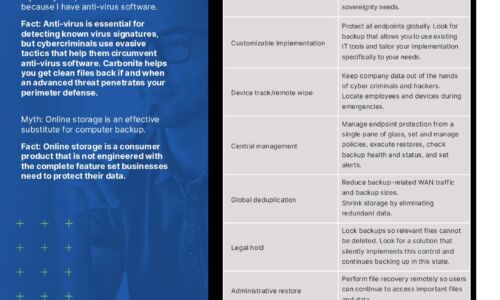
Carbonite Endpoint Protection Myths
Myth: My endpoint data is secure because I have anti-virus software. Myth: Online storage is an effective...

Unlock the Value of your Data with Simplified Database Management
If your organization is like most enterprises, your high-performance databases are supported by traditional...

5 Best Practices for Securing Modern Web Applications and APIs
Web applications are nothing new. Neither is web application security. Many businesses have been building...
Report: ICS/OT Cybersecurity 2021 Year in Review
Dragos is excited to present the fifth year of the annual Dragos Year In Review report on Industrial...
10 ways voice will disrupt the workplace in the next 5 years
The way businesses adapted to COVID-19 was nothing short of remarkable. Entire companies shifted from...
Sign up for FinTech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.