Cloud

Adaptability: The Missing Stage in Your Corporate Preparedness
Best-in-class retail and consumer organizations don't just respond to change—they stay ahead of it....

A Blueprint for Containers and Orchestration Best Practices
Containers enable agile deployment capabilities, requiring less coordination and oversight than on-premise...
Don’t Diverge—Converge
Digital acceleration is driving the adoption of hybrid IT architectures. These new hybrid environments...

Don't Diverge—Converge
Digital acceleration is driving the adoption of hybrid IT architectures. These new hybrid environments...

A Historic Opportunity for Public Sector
Discover the 8 mega trends in the public sector. Why the public sector has a golden opportunity and how...
BlackBerry Guard
Many businesses overlook or underinvest in managed detection and response (MDR), a critical aspect of...
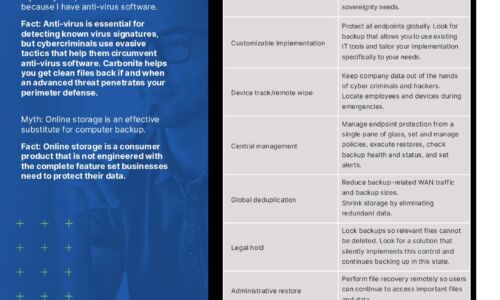
Carbonite Endpoint Protection Myths
Myth: My endpoint data is secure because I have anti-virus software. Myth: Online storage is an effective...
2021 Buyer's Guide to Comprehensive Cloud Security
Cyber resilience comes when you've secured your multi-cloud infrastructure and enabled your DevSecOps...

Advanced Threat Research Report October 2021
As 2021 progressed through its second quarter and into the third, cyber criminals introduced new—and...

MGM China Strengthens Its Defenses Against Lateral Movement
World famous resort operator gains unprecedented visibility into application traffic and workload-level...

Flexible for the future
IT decision makers are tackling a major challenge: how can we architect our IT in a way to maximise access...
Sign up for FinTech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.