Android

5 Tips for Easing Common IT Frustrations
Got IT frustrations? Who doesn't. Today, there are a few common friction-filled frustrations that arise...

Insurance MFA case study – on-premise and multiple integrations
UNIQA Czech Republic is part of one of the leading insurance groups, UNIQA, located in Austria, Central...
Multi-Factor Authentication Buyer's Guide
With the increase in phishing and data breaches over the last few years, the chances are that your login...

Make Artificial Intelligence Real
There's nothing artificial about making the world a better place. Over the last several decades, technology...
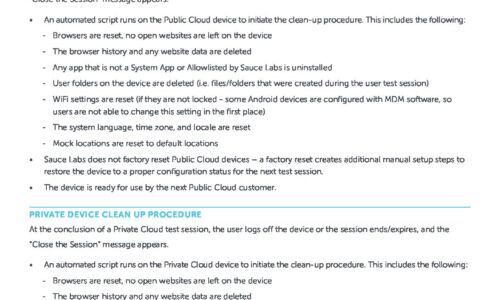
Public & Private Device Clean Up Procedure
This data sheet explains the options available when you want to make sure that your content, or some...
In-App Messages: What They Are, How They Work, and Why They Matter
We're living in a connected world. Every screen is a window of opportunity, a chance to engage with your...

The Hybrid Workplace: Adapting to the New Normal with Aruba ESP
In the past few decades, technology has shifted how we live, work, and interact with others. This mobile...

The World is Your Workplace: Public Safety Mobile Solutions
Public safety personnel of all types rely on mobile technology to remain connected, efficient and informed....
Sign up for FinTech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.