Storage Devices

Cyber Security for Dummies
Protect your business and family against cyber attacks Cybersecurity is the protection against the unauthorized...

Networking and Information Systems (NIS) Directive
The NIS Directive has been designed to work alongside data protection legislation. It will be governed...
Security Control Guide: Hardened Services Guide
System Hardening is the process of securing a system's configuration and settings to reduce IT vulnerability...
Unlocking collaboration in higher education
Collaboration and knowledge sharing are pillars of higher education. Instead of working in silos detached...
All-Flash Buyer's Guide: Tips for Evaluating Solid-State Arrays
Think Flash-First for Primary Storage. The introduction of enterprise-grade all-flash arrays has turned...

How Cloud Desktops Support Workforce Agility
How fast is the number of devices users employ growing? It has been more than four years since GSMA Intelligence...

Ransomware Threat Briefing
Cyber criminals are getting bolder and more sophisticated with their threats. No matter what kind of...

Modern Blueprint to Insider Threat Management
Taking a People-Centric Approach to Your Insider Threat Management (ITM) Programme. Insider threats can...
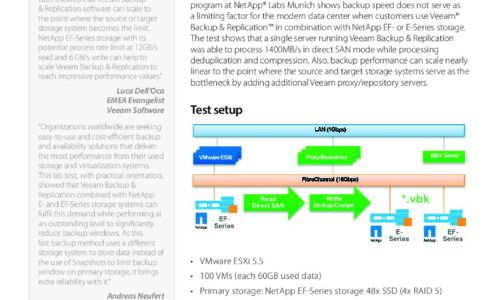
How to Build a Lightning- Fast, Multi-Petabyte Backup Repository
IT teams are facing exponential data growth. It's natural to worry about exceeding capacity, wondering...

Build smarter with tech
Your construction company wants to deliver the best, most cost-effective building projects every time,...
Sign up for FinTech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.