SAN
Enterprise Cloud Solutions
Many traditional infrastructure vendors would have you believe that hyperconverged infrastructure is...

Modern application delivery for an adaptive, reliable network
See and hear how you can streamline the delivery of apps, desktops and data into a unified, fully integrated...

Securing high tech industry network data
We all understand the negative impact of data loss, so why is it that so many organisations seem to be...

Best Practices for Deploying Huddle Rooms in the Enterprise
The 20th century was the Information Age, in which companies with access to the most relevant and timely...

Accelerate Enterprise Cloud Transformation Solution Brief
Staying competitive in today's rapidly changing marketplace demands innovating faster and delivering...
Digital Transformation: A Look Ahead
Digital transformation is reshaping organizations into digital businesses. Organizations are focused...

Find and Protect Your Sensitive Data with SQL Server Compliance Tools
This technical brief examines a database compliance and security scenario in the enterprise. It describes...

5 steps to harness the power of the organization to better serve customers
Experiences are more than just touchpoints—how customers achieve their desired outcomes is what matters. Read...

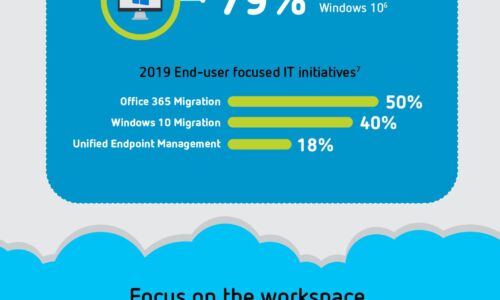
Empower End-Users With Better Experiences
Why is end-user computing innovation important? You have a lot of market forces driving your organization,...
3 Ways Emotional Connections Can Power CX
When personalization isn't paying off and data doesn't help you make sound decisions, it's time to renew...
Defending Ukraine: Early Lessons from the Cyber War
The latest findings in our ongoing threat intelligence efforts in the war between Russia and Ukraine,...

7 Ways to Work from Anywhere
Bring security and speed to the office of the future Following a massive global influx of remote work,...
All-Flash Buyer's Guide: Tips for Evaluating Solid-State Arrays
Think Flash-First for Primary Storage. The introduction of enterprise-grade all-flash arrays has turned...
Sign up for FinTech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.
