Network Security

Security Strategy Checklist
This self-assessment is designed to help you evaluate the security risks in your environment. It is intended...
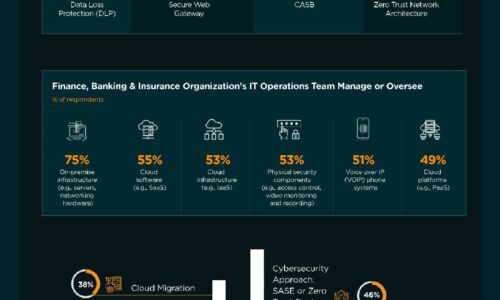
Finance, Banking & Insurance Industry | State of Cybersecurity 2021
This infographic by ISACA and HCL Technologies discusses the state of cybersecurity within the finance,...

SASE: The Network Of The Future Is Here Today
Your business can no longer rely on the old hub-and-spoke network model with its long hauls back to the...

IT’s 5 Toughest Work from Home Challenges and How to Solve Them
2020 forced the shift to a hybrid work model Unexpectedly, you found yourself working from home. The...
Forrester Wave, We’re a leader!
VMware Carbon Black Named a Leader in The Forrester Wave™: Endpoint Security Software As A Service,...

Securing Privileged Accounts: Three Steps to Maximize Protection with MFA
Hackers are eyeing your privileged accounts, so you better be using more than 'admin123' to secure them. Multi-factor...

From Seismic Disruption to a New Era of Success
No one could have foreseen the terrible impact of the COVID-19 outbreak on humankind. In business too,...

THE RISE OF AI AND MACHINE LEARNING
AI has the power to focus the volume of data in financial services. AI and machine learning tools can...

Delivering Fast and Secure Enterprise Applications
Adopting a zero trust security model — authenticating and authorizing every request, device, and user...

DDoS in the time of COVID-19
COVID-19 has caused major disruption to business on a global scale creating the perfect storm for cyber...
Sign up for FinTech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.