Network Infrastructure

Case Study - Amiri Hospital
As a leading healthcare institution in Kuwait, the 415-bed Amiri Hospital viewed its impending expansion...
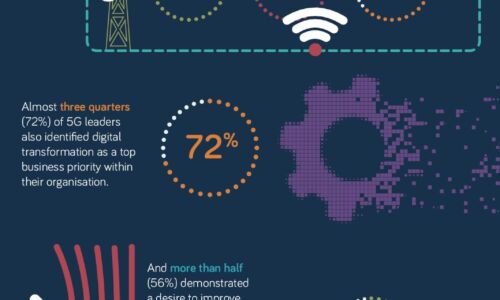
What makes a 5G Leader?
With 5G a still nascent technology, opportunity remains for businesses to accelerate adoption of this...

A Blueprint for Containers and Orchestration Best Practices
Containers enable agile deployment capabilities, requiring less coordination and oversight than on-premise...

5 Critical Considerations for DDoS Mitigation
Distributed denial-of-service (DDoS) attacks remain one of the most effective methods used by cybercriminals...
Insider’s Guide To Choosing a DNS Service
The need that DNS (the domain name system) was created to address seems simple enough: where can I find...

IDC Whitepaper: Achieving Network Modernization for the Decade Ahead
Every organization is now defined by the digital services it delivers. From engaging customers with new...
Understanding Log Analytics at Scale
The humble machine log has been with us for many technology generations. The data that makes up these...

The Business Value of VMware NSX Advanced Load Balancer
With NSX Advanced Load Balancer, teams don't have to choose between overprovisioning and potentially...
Microsoft Digital Defense Report
Over the past year the world has borne witness to a burgeoning cybercrime economy and the rapid rise...

Case Study – JUSTWork
JUSTWork wants to invigorate the concept of the workplace. For that to be possible, JUSTWork needs an...

How SASE empowers your business for the cloud generation.
Wide area networks (WANs) have played a critical role in business growth for several decades. Early WANs...
5G for the enterprise
With a desire to better understand the current, on-the-ground reality for enterprises and organisations...

Connected cities and places
Improving digital infrastructure is key to enabling a smarter city or place to develop, thereby creating...
Sign up for FinTech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.
