Mobile Computing

5G Is Changing the Game - Right Now. Is Your Infrastructure Ready?
Advanced 5G use cases will require a fundamental change in infrastructure before they can scale. As network...

Adaptive Multi-Factor Authentication
This white paper provides an overview of Okta Adaptive Multi-factor Authentication (MFA). For security...

Low Code Software Delivers Business Value
In recent years, organizations are realizing the business value of low-code software, including how they...
CIO Essential Guidance: Intrinsic Security
Despite massive spend to protect enterprise digital assets, security breaches are still on the rise....

IT and Cyber Incident Response Communication Templates
BlackBerry® Alert is a critical event management (CEM) solution designed to help organizations prepare...
A Buyer’s Guide to Optimizing Remote Employees’ Extended Network
The shelter-in-place mandates put in place earlier in 2020 sent most employees home, and for the next...
Wealth Canyon
Software companies in the financial industry, such as WealthCanyon, face challenges in collecting and...
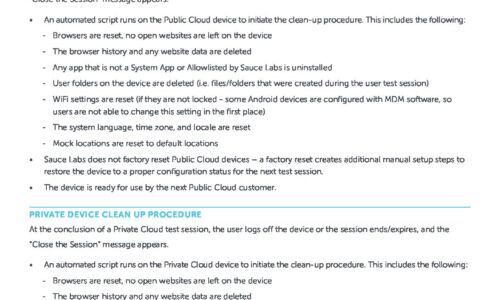
Public & Private Device Clean Up Procedure
This data sheet explains the options available when you want to make sure that your content, or some...

A Buyer's Guide to Optimizing Remote Employees' Extended Network
The shelter-in-place mandates put in place earlier in 2020 sent most employees home, and for the next...

Evaluating Modern Enterprise Storage
Rapid data growth and proliferating strategic digital business initiatives have been transforming organizations....

App Development as a Core Business Capability
Many organisations now understand the critical role that apps play in enabling their people, as well...

Securing Your 5G Edge
As service providers transition to 5G, it's important that they secure every aspect of their network....
Sign up for FinTech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.

