Malware
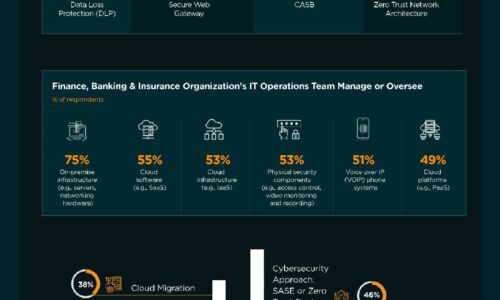
Finance, Banking & Insurance Industry | State of Cybersecurity 2021
This infographic by ISACA and HCL Technologies discusses the state of cybersecurity within the finance,...

A study of employee cybersecurity awareness in the Middle East
The cyber threat landscape in the Middle East is rapidly evolving, with cybercriminals increasingly targeting...
Cybersecurity: A Short Business Guide
The news often reports on incidents involving large corporations facing massive data breaches where the...

Part Four- Futureproofing your cybersecurity strategy
Email account takeovers are among the most insidious and damaging cyberattacks—used to invade companies...

GigaOm Radar for DDoS Protection
Cloudflare ranked higher than any other assessed vendor and is named a 'Leader' and 'Fast-mover'' in...
Hidden Costs of Endpoint Security
When it comes to endpoint security, CISOs are in a bind. Most assume that endpoints will be compromised...

Retail eBook
Modern MFA For Retail's Hybrid Workforce Modern retail organizations are moving data to the cloud while...
The State of Threat Prevention: Evasive threats take Center Stage
Digital transformation has rendered many traditional security solutions useless in the face of modern...

Top 5 Ways to Simplify Data Protection with Microsoft Azure
Read this white paper to find out five ways that you can simplify data protection with Microsoft Azure,...

How Effective Retailers Balance Customer Engagement and PCI Compliance
For CIOs of retail organizations, compliance with Payment Card Industry (PCI) standards is a top concern,...

The Business Value of Storage Solutions from Dell Technologies
In the era of digital transformation — the evolution toward much more data-centric business models...
Sign up for FinTech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.