Event Management

SD-WAN in the Age of Digital Innovation
Achieving Business Agility While Reducing Disruption. Most organisations are in the midst of some form...
SaaS Security Solution Checklist
SaaS applications have provided tremendous value to end users due to their easy setup and collaboration...

The Total Economic Impact™ Of The CB Predictive Security Cloud
Your endpoints are one of the most targeted assets in your organisation. In 2017 alone, more than 50%...
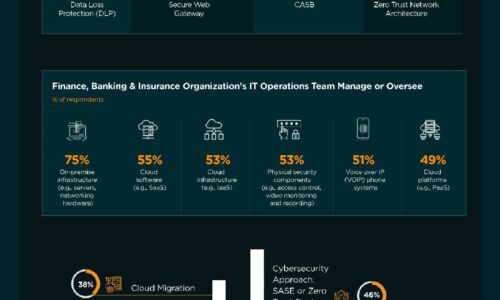
Finance, Banking & Insurance Industry | State of Cybersecurity 2021
This infographic by ISACA and HCL Technologies discusses the state of cybersecurity within the finance,...

Rebellions and rejections report
The global pandemic forced organizations to pivot rapidly from an office-based workforce model to one...

Why Corelight Is Your Best Next Move In Enterprise Security.
Despite spending billions annually on security infrastructure and services, even the most sophisticated...

Replace AV Buyer’s Guide
Today's businesses face a unique set of security challenges. Many organizations know their current antivirus...
Ponemon Cost of Insider Threats Global Report
Independently conducted by Ponemon Institute External attackers aren't the only threats modern organisations...

Top 3 Challenges Your Team Faces When Building in the Cloud
Today's cloud and security teams are asked to do more with less. Although the capabilities and cost of...

10 Endpoint Security Problems and How to Solve Them
Companies are facing massive cybersecurity challenges – many of which are rooted in the endpoint. In...

IT and Cyber Incident Response Communication Templates
BlackBerry® Alert is a critical event management (CEM) solution designed to help organizations prepare...

The Future of Secure Communications
How BlackBerry's SecuSUITE is changing the way governments and enterprises communicate. In an increasingly...

The State of Application Security in 2021
Barracuda commissioned independent market researcher Vanson Bourne to conduct a global survey of 750...

Security Operations Use Case Guide
Responding to security incidents and vulnerabilities is an ongoing process, and you know that reacting...
Sign up for FinTech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.