ERP

Modern Blueprint to Insider Threat Management
Taking a People-Centric Approach to Your Insider Threat Management (ITM) Programme. Insider threats can...
All-Flash Buyer's Guide: Tips for Evaluating Solid-State Arrays
Think Flash-First for Primary Storage. The introduction of enterprise-grade all-flash arrays has turned...

Illumio CloudSecure: Cloud-Native Security Simplified
Gaining unified visibility into application traffic across multi-cloud, hybrid cloud and data center...
Zero-Trust is the Outcome of Identity-Based Access Control
As the IT landscape evolves, new and more sophisticated cybersecurity threats continue to appear. These...

Practical Guide To A Zero Trust Implementation
Zero Trust is becoming the security model of choice for enterprises and governments alike. However, security...

Disaster Recovery in the Cloud with Cloud Volumes ONTAP
In this whitepaper, NetApp examines in detail the challenges involved in setting up a DR environment,...
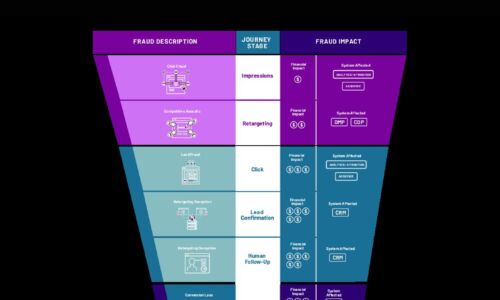
Cybercrime Threatens the Digital Funnel
Cybercriminals are employing new attack methods on new digital surfaces, including digital marketing....
Empowering Developers Through Cloud Services
The enterprise is under tremendous pressure when it comes to modern application deployment. The industry...

Ransomware Protection with Veritas NetBackup Appliances
Download this whitepaper to discover how to protect your backup and recovery infrastructure from attacks....

3 steps to accelerating innovation with low-code app development
Digital transformation can put a heavy burden on your app development. You must reduce your backlogs...

Take control of diverse and rapidly evolving enterprise risks
Today's enterprises face diverse and rapidly evolving risks, including expanding regulatory requirements,...
Sign up for FinTech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.


