Endpoint Security

Unified Endpoint Management (UEM): Address 3 Common Challenges
With digital transformation comes mobile devices, apps and high-speed connectivity that make it possible...

Safety First: The Face of Cybersecurity in Today's Workplace
As working environments and styles change, organizations must adapt IT to keep devices secure. The digital...

Deploying Consistent Application Services in Multi-Cloud Environments
Most organizations prioritize cloud flexibility—and let application teams choose the best environment...

Why automation is essential for cyber resilience
Digital transformation makes today's businesses more productive and more vulnerable to cyberattacks....

Shift your Web Security to the Cloud, for the Cloud
As enterprises embrace digital transformation, the adoption of software-as-a-service (SaaS) is robust...
Modern upgrade opportunities powered by Veeam DataLabs
With the upcoming end of life of Microsoft Windows server 2008 R2, organizations need to have a plan...

Executive Brief: The Ransoming Of Higher Education
Coordinated attacks are hitting higher education institutions across the nation and around the world....

Solve the security puzzle with end-to-end security solutions
As an IT decision maker, you're focused on finding effective solutions you can implement quickly and...

Multi-Vector Protection
Educating users is an undeniably effective way to protect them from phishing and other malware, but it...

The Critical Importance of Securing Government Smart Buildings
Over 50% of governments currently have smart building technologies in pilot or production. By 2023, 20%...

Isolated Castles: Incident Response in the New Work From Home Economy
Since the shift to work from home, there's been a paradigm shift in the IT and security industry. The...
Forrester : Managing Security Risk and Compliance
The explosion of data and proliferation of devices demands better security tools and monitoring from...
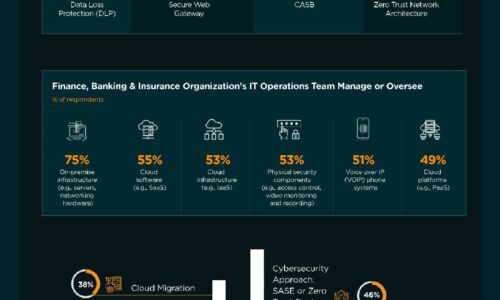
Finance, Banking & Insurance Industry | State of Cybersecurity 2021
This infographic by ISACA and HCL Technologies discusses the state of cybersecurity within the finance,...
Sign up for FinTech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.
