Compliance

The Book of Knowledge - HAandLC
Gartner predicts that 65% of all app development activity will take place on low-code platforms by 2024....

14 innovative personalisation ideas for the digital-first customer
Prior to 2020, customer personalisation was a nice thought. However, the global pandemic shifted everything....

Key Storage Considerations in Determining Optimal Workload Placement
In early 2020, IDC performed in-depth primary research on how organizations determine workload placement...

Compromise Assessment Use Cases
With cyber attacks increasing both in quantity and sophistication, how can an organization know with...

The Only Certainty is Uncertainty
We cannot anticipate change, although we can bet on its coming, be it from weather, pandemics, socio-political...

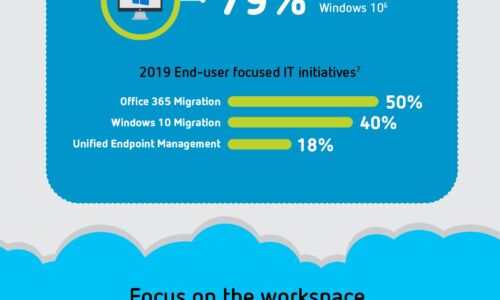
Protecting The End User
A people-centric approach to managing vulnerability, attacks and privilege. Organisations are spending...

MetriStar Top Provider Award Contact Center Platforms
RingCentral has earned the Metrigy MetriStar Top Provider Award for contact center platforms. The value...
CIO Perspectives Magazine issue 7
Business continuity for CIOs, explained. Legacy systems weren't built for the pace of change that CIOs...
Sign up for FinTech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.