Cloud

Practical Guide To A Zero Trust Implementation
Zero Trust is becoming the security model of choice for enterprises and governments alike. However, security...

Encryption Is Now a Trojan Horse: Ignore It at Your Peril
The game of leapfrog between hackers and data security professionals continues. No sooner do organizations...
5 Ways that SD-WAN Transforms your Network
SD-WAN transforms your network by making it more responsive, providing greater bandwidth and being more...
Application Control for Dummies
Application control, sometimes called application whitelisting,is a means for controlling the software...
Complete Cloud Security for Professional Services
Thales have a long history in securing some of the world's most sensitive data, and professional service...
A CIO's Strategy Framework for Disruptive Transformation
This is a whitepaper by IDG on behalf of Adobe. Today, we don't know how we will return to our workplaces,...
Reimagining IT service delivery and operations in unimagined times
Discover the top 3 ways adding Operation Management to your ITSM strategy can help your business be more...

How to Build a Cyber-resilient Business Ready to Innovate and Thrive
This eBook discusses if, and to what degree, an organization's adoption of a strong cyber-resiliency...
Visibility in Action
Powering end-to-end insights across customer experience, satisfaction, and cost management. Leading companies...
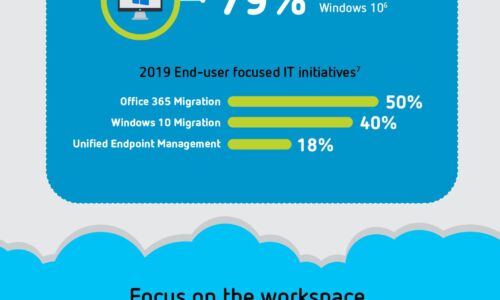
Digital Transformation: A Look Ahead
Digital transformation is reshaping organizations into digital businesses. Organizations are focused...
API Security Best Practices
Application Programming Interfaces, or APIs, were developed to streamline the way digital ecosystems...

The Road To Digital Experience Success
The world of work is not changing. It has already changed. Firms that have not boarded the ship need...
Sign up for FinTech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.

